Facilities and services, throughout Catalonia. Headquarters in Barcelona.
For more than 40 years , we have traveled a path full of innumerable challenges, with blind confidence in our work, seriousness and maximum professionalism . From the beginning, we have tried to differentiate ourselves as a local company from the large multinationals, “giving a personalized service” , since each Client is different and special, not a number.

The Post-sale Service is a quality that distinguishes us, since we carry it out for all the brands in the sector , as well as ongoing advice to all our Clients.

We offer Security, Tranquility and Control.
We capture the needs of our Clients, and advise them the best options for their needs
Anti-intrusion systems
Once the alarm system is activated, it is activated automatically. For example: If intrusion is detected in a certain area, it can give the acoustic or optical signal or send a warning message to one or more numbers.
If the presence of smoke, heat or both is detected, send a message to the “monitoring service” or activate the sprinklers on the ceiling, to put out the fire. If the presence of toxic agents is detected in an area, close the doors so that the problem does not spread, etc. etc.
Parts
- Processing center
- Keyboard
- Exterior siren cabinet
- Motion detectors (PIR)
- Inertial or seismic sensors
- Glass break detectors
- Lapa (thermovelocimetric detector)
- Fallen persons detector (dead man)
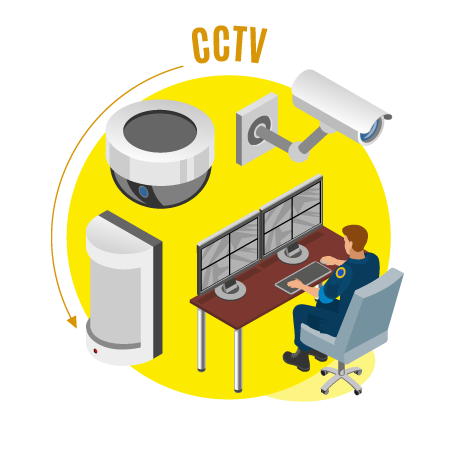
CCTV cameras
Closed circuit television or CCTV (acronym in English for closed circuit television) is a video surveillance technology, designed to monitor a variety of environments and activities.
It is called a closed circuit, since unlike what happens with diffusion, all its components are linked. Furthermore, unlike conventional television, this is a system designed for a limited number of viewers.
FEATURES
The circuit can simply be composed of one or more surveillance cameras connected to one or more video monitors or televisions , which reproduce the images captured by the cameras. Although, to improve the system, they are usually connected directly or linked by network to other components such as videos or computers
If the presence of smoke, heat or both is detected, send a message to the “monitoring service” or activate the sprinklers on the ceiling, to put out the fire. If the presence of toxic agents is detected in an area, close the doors so that the problem does not spread, etc. etc.
- PTZ (pan-tilt-zoom)
- Night vision
IP cameras
IP video-surveillance is a visual surveillance technology that combines the analog benefits of traditional CCTV (Closed Circuit Television) with the digital advantages of IP (Internet Protocol) communication networks, allowing supervision local and / or remote images and audio, as well as the digital treatment of images, for applications such as license plate recognition or facial recognition, among others.
Most of the most modern facilities are abandoning analog technology in favor of IP video surveillance, given its versatility, functionality, simplicity and optimization of the company’s existing infrastructures.
The most outstanding advances
- Wireless capabilities that even eliminate cable runs, include the high image resolution offered by megapixel cameras (1.3 megapixels ...)
- The inclusion of intelligence systems for video processing and event management or digital counters. It is possible to capture video and store it at a few frames per second or activate the recording only in certain circumstances, either by detecting movements in a certain area or by time bands.
- High compression rates to avoid high bandwidth and storage space consumption, with standards such as H.264, which significantly simplify storage in NVRs (Network Video Recorders)
- Video servers compared to other formats such as Motion JPEG, MPEG-4 video.
These technological advances have led consultants such as IP Video Market, in their report ‘Video Surveillance Market Size and Forecast Guide 2010’, to estimate that the IP video surveillance market will exceed that of CCTV (analog), with a growth of 200%.
Security and Surveillance Monitors
Control for the theft committed by the company’s own employees, as well as by outside employees related to work, which is also understood as internal theft, because suppliers and subcontractors often have the same access privileges as the company’s own employees .
Statistically there are fewer thefts or fraud internally than externally; but since they are usually large amounts, the overall figure increases considerably, equating to losses due to external theft.
Alarm receiving center
It is the control center for the reception, monitoring and verification of the signals issued by the Security System 24 hours a day.
If the veracity of the alarm is verified, the Police, Security Service or pertinent emergencies are immediately notified.
Video-Analysis Security
When the cameras detect a new event through the video analysis software, they send the analysis to the server, which generates an alarm. This alarm can be of various types: sound with siren, light alarm, sending email to mobile or all at the same time.
Video-analysis comes from being used in the military sector, in the storage of toxic substances, of great value, protection, etc. etc. Therefore, it is classified as high perimeter security.
- Perimeter security
- Marketing actions
- License plate recognition
Optical fog
In a few seconds, the Mist Generator fills the room with a dense and harmless Security Fog, so that it is impossible for the thief to see his own hand in front of his face.
We are talking about practically in a scarce minute, he cannot be distinguished at 40 cm
Mist generator
Highly recommended for jewelers, tobacconists, opticians, and any company vulnerable to theft
Three words that define next-generation anti-theft protection – Security Fog. Unlike surveillance cameras, the Security Fog instantly stops thieves. The Mist renders them unable to see, completely disorienting them.
In short, a thief will never be able to steal what he cannot visualize.
The Safety Fog in large spaces as in confined spaces
There is practically no product or premises that cannot be protected by the Safety Fog. Every day our Fog Generators protect companies of all sizes around the world. They avoid big losses, high insurance company premiums, and unpleasant experiences caused by theft and vandalism. (It is approved in more than 40 countries).
The Safety Fog is similar to smoke, but, the Fog is completely safe and harmless and also, accidentally caused shots can be easily avoided.
Real-time demo: http://youtu.be/JpcgURFucdU
Fire protection
It is the system for detecting the outbreak of fire that gives notice of the place where the incident occurs. They can be classified into:
Conventional systems , for small places.
Analog systems , are those that allow to determine the point where the outbreak of fire occurs.
Detection is the first step in the event of a fire, since it can activate the alarm system, the extinguishing system or both at the same time.
Firefighting
They are the systems to put out incipient fires. They can be automatic or manual.
Fire extinguishers: powder – Co2 – automatic – etc ..
Fire hydrants equipped (bias) complete hoses with metal cabinet connected to a water outlet.
Fire classes
- Wood, charcoal, fabrics, plastics, etc.
- Gasolines, oils, paints, etc.
- Propane, methane, city gas, etc.
- Metals, minerals, magnesium, sodium, etc.
We use equipment from the best brands on the market, with an optimal quality-price ratio.
We provide rental services.
The project that started in the abc of alarms with great enthusiasm, thanks to new technologies has become a constant evolution on cctv, ip cameras, sophisticated anti-intrusion, detection and fire protection, video-analysis, etc.
Protect yourself against theft and feel more secure

Our technical team and human personnel, give the personalized treatment that differentiates us from other companies.
Security Consultants

We hurry and worry about solving any incidence of other brands, (be it due to bad after-sales service or failure of the installations carried out), and thus be able to become their security consultants for their advice and make them Clients and Friends.